Nearly every day we hear of another ransomware attack against a public or private institution. In fact, the numbers are much higher. In the first half of 2021, more than 2,000 attacks were reported to the FBI in the U.S. alone, a 62% increase from the same period in 2020. And it’s impossible to know how many more attacks were never reported. With this surge, total damages are rising as well. Estimates by Cybersecurity Ventures project ransomware damages will reach $20 billion by the end of 2021 and a whopping $265 billion by 2031. But it doesn’t have to be this way.
Download our new report, “Stopping Ransomware Attacks with True Runtime Protection” to learn about some of the key factors that contribute to the success of ransomware attacks, as well as recent initiatives and innovations that enable defenders to take power back from attackers. We look at how ransomware is evolving, the technologies that are effective – and not effective -- at stopping ransomware and why, the decision to pay or not to pay the ransom, the impact of cyber insurance, and the role of the U.S. government in addressing the crisis.
Here are just a few takeaways from the report:
-
Ransomware is most damaging when it moves laterally from desktops to servers, which are online 24/7/365 and house all the critical applications and data necessary to keep an organization operational. Adding complexity to remediation and response, ransomware attacks now involve double extortion tactics – threatening to leak infiltrated data if the victim doesn’t pay the ransom.
-
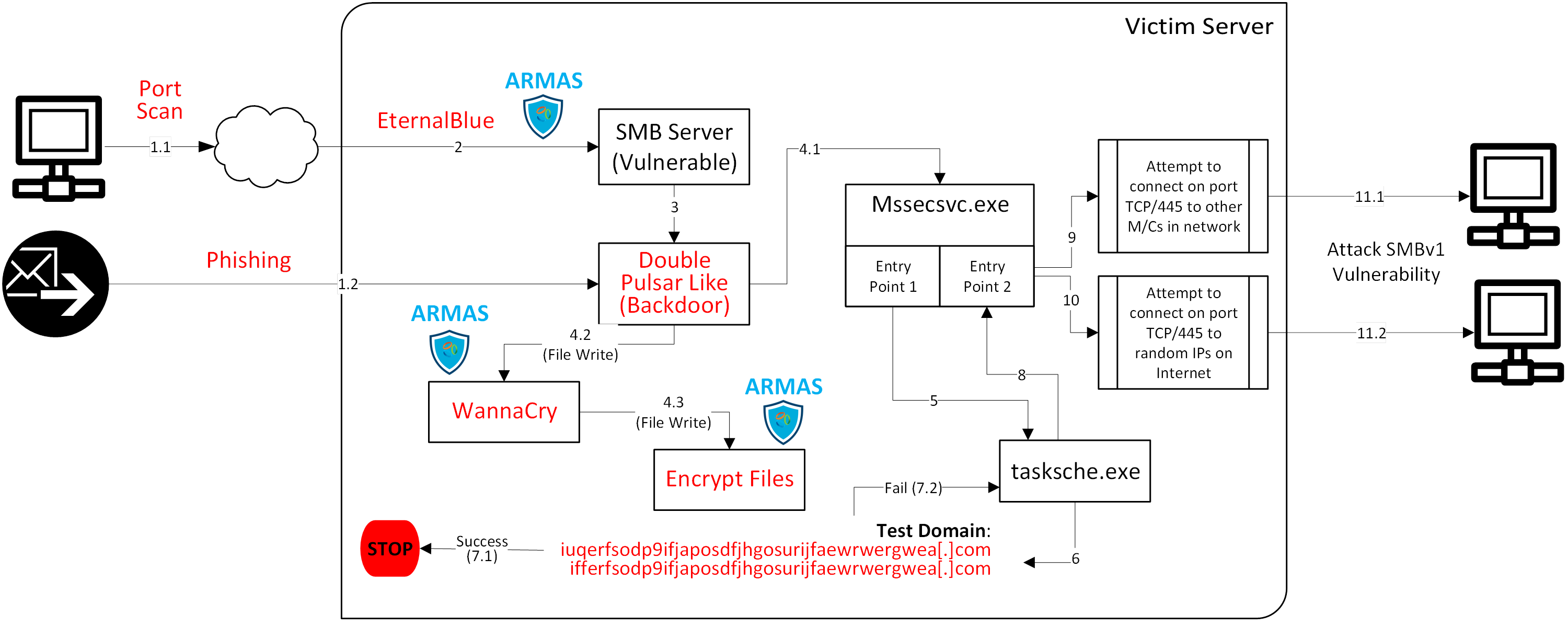
More than 75% of companies infected with ransomware are using endpoint protection products (EPP) or endpoint detect and response (EDR) tools that they believe could help stop attacks, when in fact these tools do not. Ransomware attacks are leveraging multi-step kill chains, deploying file-less malware, and using remote code execution (RCE) techniques that are bypassing these conventional, probabilistic security controls.
-
Victims of ransomware that decide to pay the ransom are rarely able to retrieve all their data and, the majority that do pay, are often hit again with another ransomware attack, sometimes by the same group that executed the first attack. But the decision to pay or not may soon be a moot point for organizations located in states that are considering prohibiting ransomware payments.
-
More organizations are opting for cyber insurance but expect it to become more costly and difficult to attain. And it is far from a silver bullet solution. In fact, some research indicates the practice encourages cybercriminals as policyholders are more likely to pay the ransom.
-
The world runs on software, yet application runtime remains one of the most vulnerable attack surfaces in any organization. Ransomware attacks repeatedly target applications and workloads most vital to the business, so we need to secure our organizations by protecting the software workload while it is running, wherever it is running. Ensuring attackers cannot exploit critical applications to run malicious code, is the only way to eliminate ransomware threats.
Download the report for more details on the multi-faceted challenges of ransomware and what you need to know to better mitigate risk and stop attacks before they start, or read how to prevent ransomware breaches in healthcare.