By Satya Gupta, Founder and CTO, Virsec
Over the July 4th weekend, the REvil ransomware syndicate hit software supplier Kaseya Ltd. and crippled more than 200 United States companies. The criminals took advantage of a reduced weekend security workforce to infiltrate up to 1,500 businesses globally, according to Reuters. That number is sure to fluctuate as more information develops.
The Russian-linked ransomware group encrypted entire networks in the Kaseya supply chain and demanded $70 million in cryptocurrency to deliver a universal decryptor key. REvil claimed more than a million individual devices were infected in what is believed to be the biggest ransomware attack to date.
The White House, FBI, and Department of Homeland Security quickly sprang into action, initiating a detailed investigation into the crime and assisting victims of the attack. Anne Neuberger, Deputy National Security Advisor for Cyber and Emerging Technology, urges anyone who believes their systems have been compromised in the Kaseya ransomware incident to immediately report it to the Internet Crime Complaint Center.
Infiltrating the Supply Chain to Deliver Ransomware
Kaseya Ltd. provides network management software, and its virtual systems/server administrator (VSA) product was targeted to spread the ransomware through Kaseya's managed service provider customers.
Just as the attack on the SolarWinds supply chain targeted a third-party software provider installed throughout enterprises and infected its customers, the REvil malware spread to customers by exploiting vulnerabilities in its VSA software. As the software was deployed by the customer, the malware automatically spread laterally through the software infrastructure.
The Associated Press reported that Fred Voccola, CEO of Kaseya, said only a small percentage of its 37,000 customers were compromised. But of those 50 or 60 compromised, “70 percent were managed service providers who use the company’s hacked VSA software to manage multiple customers. It automates the installation of software and security updates and manages backups and other vital tasks.”
Kaseya quickly posted an alert for its customers on July 2, 2021, and stated that its security team would continue to work around the clock in all geographies to resolve the issue and restore its customers’ service, providing updates as they become available.
Zero-Day Attack Confirmed
As of July 6, 2021, Kaseya confirmed that REvil exploited a zero-day attack on its software code. Kaseya posted the incident overview and technical details on its website. The investigation is ongoing, and the company will provide more information on this link as it becomes available.
Kaseya reported that on July 2, 2021, the company received reports from customers that they detected ransomware executing on their endpoints. Kaseya confirmed that the attackers were “able to exploit zero-day vulnerabilities in the VSA product to bypass authentication and run arbitrary command execution. This allowed the attackers to leverage the standard VSA product functionality to deploy ransomware to endpoints.”
Kaseya listed the specific Indicators of Compromise (IOCs), which included network IOCs, web log indicators, endpoint IOCs, as well as the files that were used as part of the deployment of the encryptor.
Kaseya is configuring an additional layer of security to its Software as a Service (SaaS) infrastructure that will change the underlying IP address of the VSA servers and provide a patch. As of July 7, 2021, the update has not been released due to an unresolved issue, according to Kaseya’s security team.
Customers can download Kaseya’s VSA Compromise Detection Tool for their networks and stay tuned to the Kaseya Help Desk for the latest developments.
A Closer Look at the REvil Ransomware Group
REvil, also known as Sodinokibi, is a notorious Ransomware-As-A-Service (RaaS) gang. The criminals were behind the ransomware attack on global meat processer JBS in May 2021, where they netted a reported $11M in ransom.
REvil favors two kinds of modus operand: phishing attacks on personal endpoints and exploits on publicly disclosed vulnerabilities that have not been patched to gain access to an organization’s IT infrastructure.
REvil leases the malware it creates to affiliates on the black market, who use it to hit targets of their choosing – ideally those who have not had time to apply the necessary updates to web-facing software, leaving them exposed. After extracting the ransom, the affiliates share a percentage of their earnings with REvil.
REvil can also encrypt a user’s files to gain administrative access to a direct target by exploiting a privilege escalation vulnerability such as in Oracle WebLogic (CVE-2019-2725) or in Windows (CVE-2019-8453). The group has been known to infiltrate networks and steal sensitive data prior to an attack. The criminals then use the threat of exposing that data as extra incentive for their victim to pay the ransom.
REvil’s Supply Chain Ransomware Attack Technique
Let’s review how the ransomware attack on Kaseya and its supply chain unfolded:
The attacker infiltrated Kaseya and/or its customers’ infrastructure via a zero-day vulnerability in Kaseya’s VSA code. Exploiting this vulnerability allowed the attacker to obtain administrative access and set up a reverse channel back to their command control center. Next, the attacker used the reverse channel to drop and execute the REvil malware on the victim’s infrastructure.
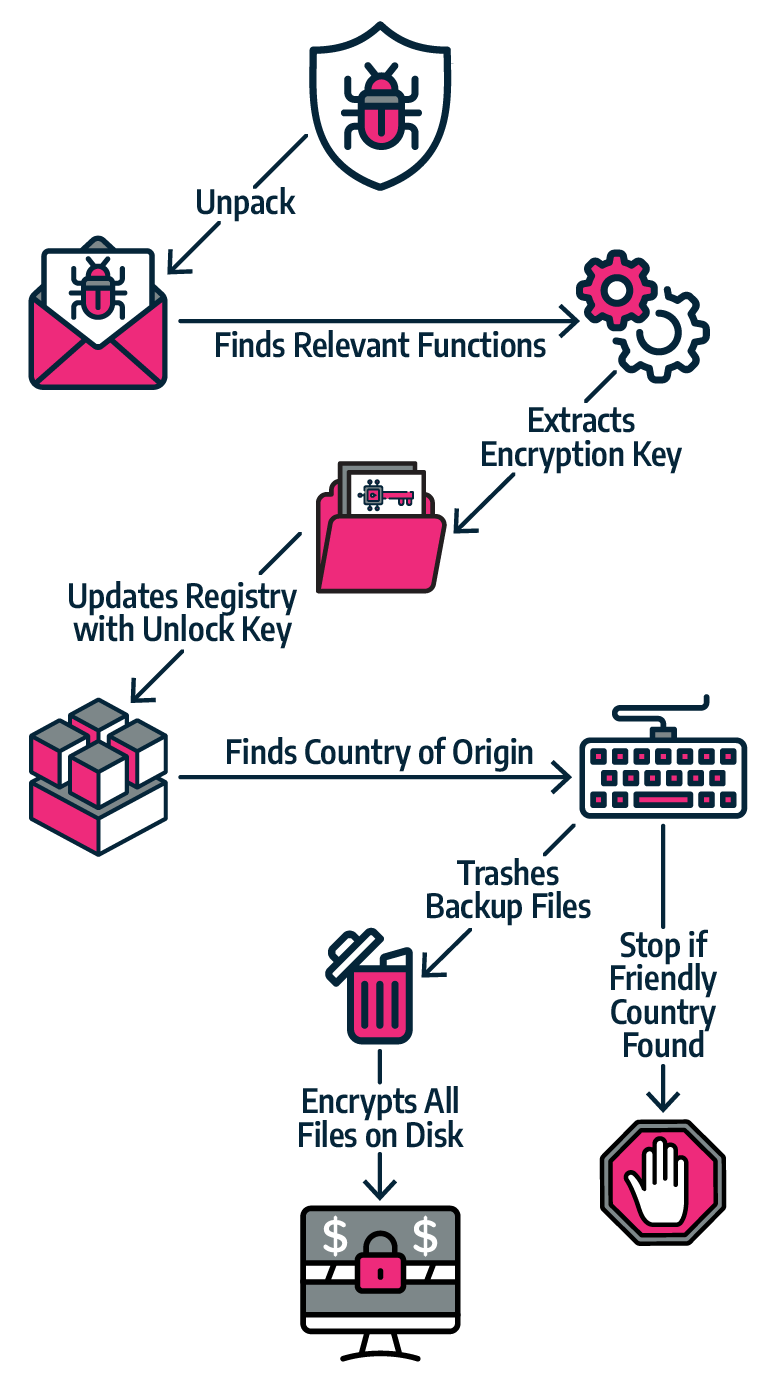
These operations are summarized in the diagram below:

REvil Ransomware Operation
Once the packed REvil malware is dropped and executed on the victim’s compute, the malware unpacks and constructs the active REvil code directly into memory. Next, it extracts the encryption key from a config file. This key is also buried into the Windows Registry key for persistence. Next, REvil determines if the victim is from a friendly country or not. It stops if the victim is from a friendly country. If the victim is not from a friendly country, the malware wipes all backups, encrypts the storage all backups, encrypts the storage, and raises the ransomware demand. If the victim fails to pay the ransom in the stipulated time, the attacker threatens to make confidential information it collected prior to encrypting the disk, public. If the victim does pay the ransom, the attacker supplies the decryption key.
Application-Aware Ransomware Protection
Virsec Security Platform’s (VSP) unique application-aware protection keeps critical software, including OS Services, first and third-party software and applications safe at runtime even if they are unpatched or have unknown vulnerabilities lurking in the code.
As the ransomware attack attempts to kick off, VSP automatically recognizes that attacker-produced or attacker-influenced code is attempting to execute and immediately stops it without even a single instruction executing. VSP relies on legitimate application code as the source of truth, so it does not require prior knowledge of threats.
As legitimate code executes, Virsec’s patented AppMap® technology automatically maps and monitors actual code execution. Therefore, if an application attempts to deviate from its AppMaps, VSP instantly treats the deviation as a threat and blocks further execution. The attack is then stopped in the first steps of the kill chain as VSP prevents known and undisclosed vulnerabilities from being exploited.
Deterministically Disable Ransomware
VSP deterministically disables ransomware weaponization steps with a unique Process Monitoring capability in VSP Host. Subsequent activities, such as shell code execution, are inactivated, and any attempt to change files on disk are detected and reversed.
By deploying and configuring VSP Host with its significant File Signature Database capability, VSP ensures that only intended software will run. Any other software, including file or fileless malware, is fully blocked before it executes. If a network is already infected with ransomware, VSP can be installed to locate malware lurking in an organization’s infrastructure.
Take Immediate Action
Cybersecurity and Infrastructure Security Agency (CISA) issued guidance for effected customers, encouraging organizations to review the Kaseya advisory and immediately follow their guidance to shutdown VSA servers. CISA recommends taking immediate action to implement the following cybersecurity best practices:
-
Ensure backups are up to date and stored in an easily retrievable location that is air-gapped from the organizational network
-
Revert to a manual patch management process that follows vendor remediation guidance, including the installation of new patches as soon as they become available
-
Implement:
-
Multi-factor authentication; and
-
Principle of least privilege on key network resources admin accounts
Want to Learn More?
Schedule a demo to see Virsec Security Platform defend against attacks in real-time.

