Although file-based allowlisting has held the reputation of being the gold standard of cybersecurity, poor implementations and the difficulty of operationalizing in the past have limited its adoption. However, the tides are turning with the emergence of Zero Trust principles, including SBOMs. But before we dive deeper into what's causing this shift, let's explore where things went awry in the past.
Overly Complex and Manual
Previous attempts to solve this problem required significant initial and ongoing investments.
- Failed to see the forest from the trees: Workloads typically contain 150,000+ executable files, and file-centric approaches quickly became a logistical nightmare. These solutions failed to recognize that software vendors deliver packages, not individual executables, and enterprises install packages rather than the hundreds of executables in the package. For example, when installing MS Word on your laptop, a user would start with the software package, not the thousands of executables that MS Word will ultimately install in the MS Words folders. Given an executable, it is tough to discern which software package it came from. Establishing trust one executable at a time is challenging when preparing a workload for first use and when the enterprise patches the workload.
- Did not leverage automation: Given the sheer volume of files in each workload, compounded with the high volume of workloads in an enterprise and their constant updates and patches, implementing allowlisting without automation is impractical and unachievable.
Limited Efficacy / Value
Despite the significant investment required to deploy and maintain allowlisting solutions, they yielded few meaningful outcomes bringing the value into question.
- Simplistic Assumptions: Past allowlisting approaches have relied heavily on "policies," which are assumptions malicious actors love to target. Take, for instance, the allowlisting policy that designates all executables in a "trusted" directory as legitimate. A cunning attacker could easily drop malware into such a directory and have it go unnoticed. Or consider a policy wherein a file that has been present on many workloads and for a sufficiently long time must be pristine. A savvy attacker could alter the file's timestamp and distribute it to many systems to evade detection.
- No runtime protection: Trusted code can launch child processes using another executable, and attackers can exploit this capability by manipulating the child process arguments to run code of their choosing. Past allowlisting solutions could not stop rogue child processes, especially when faced with "fileless" attacks – one where one or more arguments passed to the child process were command strings.
What's New And Different Now in Allowlisting
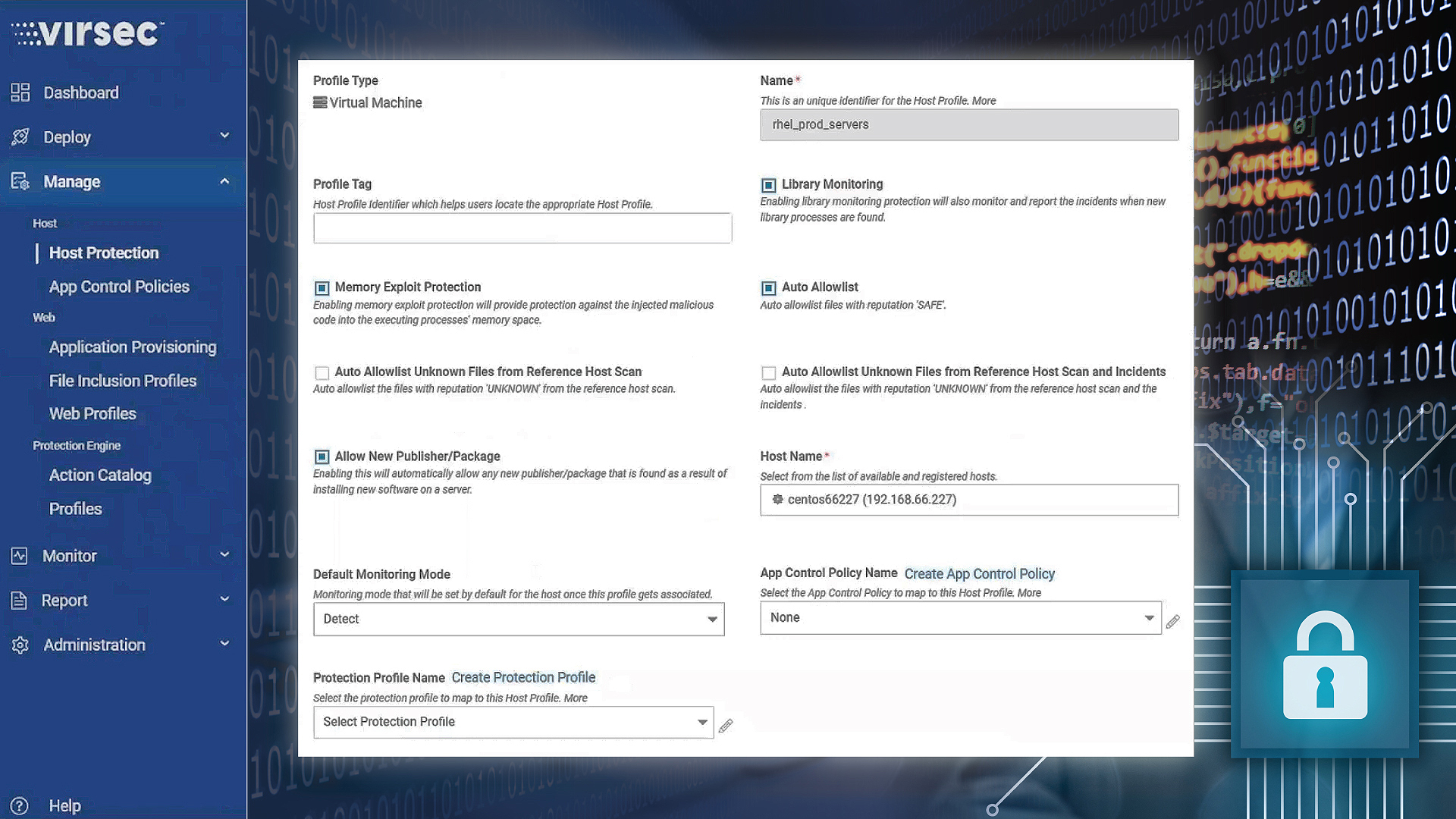
Virsec's Zero Trust Workload Protection (ZTWP) implementation addresses the problems in the preceding solutions of allowlisting through the following approach:
Highly Automated Operations
- Focussing on the forest rather than the trees: By creating a list of software packages (OS, RPMs, MSI, tarballs, zip files, etc.) with their corresponding URL, it is simple to verify the provenance of the packages and all the files derived from them. A modern zero trust allowlisting solution ensures the legitimacy of the publisher of each software package, a critical element for preventing the execution of malicious code.
- Automated with SLA: Virsec's allowlisting model integrates directly into the enterprise software deployment tools to establish provenance during the initial deployment and as the enterprise deploys new code to the workload.
Unbeatable Runtime Protection
- Chain of Trust: Extending the chain of trust directly to the code developer obviates the need to depend on policies. This thought process aligns with the recent focus on SBOMs and avoids the creation of policies based on assumptions that malicious actors can easily bypass.
- Continuous Runtime Protection: Modern allowlisting solutions provide runtime security by ensuring that even child processes spun out of legitimate code are legitimate. Today's zero trust allowlisting solutions ensure that both parent and child process(es) continue running the original pristine code and never executing injected code or falling victim to "fileless" attacks because the allowlisting model extends beyond files into process interactions.
Summary
Modern Zero Trust for Workload Protection (ZTWP) overcomes the complexity and lack of precision inherent in yesterday's file-based allowlisting solutions. By tying trust to packages, it is easy to deliver a highly automated model that is policy-free but based on deterministic concepts such as provenance, authorization, and integrity of executables. The end-user no longer must deal with subjective policies and collect metadata for every application. Additionally, the Zero Trust for runtime processes delivers protection from very difficult-to-detect attacks, such as "fileless" and memory injection attacks.
Allowlisting remains the gold standard of cyber protection, and Virsec has addressed the historical issues that plagued allowlisting solutions of the past. Given that EDRs are weak in protecting against real-time zero-day attacks, it may be time to try Virsec's ZTWP.
To know more about today's Zero Trust for Workload Protection, please visit our website: www.virsec.com