Ransomware Hit Against Epiq Attacks Web & Managed Services
The ediscovery and web service firm was struck by Ryuk ransomware last week, forcing it to take its systems offline. Ryuk is known for its destructive crypto-ransomware, where it encrypts its victims files, thereby blocking access until the victim caves to the ransom demand.
If the victim doesn’t cave to the demand, Ryuk attackers have already demonstrated they’re willing to escalate the terms to coerce cooperation.
A legal reporter shared the news on March 2 that Epiq had taken their systems offline after their devices were being encrypted by Ryuk ransomware. Epiq’s legal clients were unable to access their files and documents through their e-Discovery platforms, files needed for court cases and other deadlines.
Epiq itself released a statement, saying they took their systems offline to prevent the threat from worsening.
"On February 29, we detected unauthorized activity on our systems, which has been confirmed as a ransomware attack. As part of our comprehensive response plan, we immediately took our systems offline globally to contain the threat and began working with a third-party forensic firm to conduct an independent investigation.
Our technical team is working closely with world class third-party experts to address this matter, and bring our systems back online in a secure manner, as quickly as possible.
Federal law enforcement authorities have also been informed and are involved in the investigation.
As always, protecting client and employee information is a critical priority for the company. At this time there is no evidence of any unauthorized transfer or misuse or exfiltration of any data in our possession."
Reports later that day revealed all 80 of Epiq’s global offices and computers had been affected by the attack.
How Ryuk Invaded Epiq
At the end of last year in December, TrickBot malware invaded an Epiq computer. An Emotet Trojan is a common way for attackers to download TrickBot, and it’s usually injected into a user’s system via a phishing email.
TrickBot malware harvests things like passwords and cookies from the victimized computer and then invades the network laterally, gathering more data as it goes. TrickBot can then open access to the attackers using a reverse shell. From there, the Ryuk operators have access to the infected computers and can spy on the network, performing activities such as continuing to steal login credentials – particularly administrator credentials. Then, they use PowerShell Empire or PSExec to launch the ransomware onto the network devices.
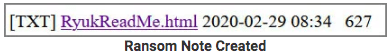
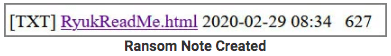
For Epiq, the bad actors distributed Ryuk ransomware through Epiq’s network on Saturday morning, February 29, 2020. The ransomware started the process of encrypting data and files on the impacted computers. During encryption, a ransom note is created, named RyukReadMe.html, like the image below, and placed in every folder. Every encrypted file is altered to have a .RYK extension.
Some of the Habits of Ryuk Threat Actors
Ryuk has been around since August 2018 but it’s earning itself a growing fearsome reputation since Christmas 2018. It’s increased the nastiness of ransomware considerably by adding on extortion-type threats on top of ransom demands.
Ryuk is known to go after large enterprise, seeking big ransoms. Malwarebytes reports attackers behind Ryuk usually go after ransoms ranging from $97-$320K. In our blog last December (2019), In 2019, the Year of Rising Ransomware, Ryuk Wields its Own Unique Nastiness, we noted that this practice is called Big Game Hunting. We also described that typically this kind of campaign is rolled out in stages, often beginning with a phishing attack, just as this one did. The attackers seek to gain user credentials to get into the organization’s network where they can then survey the asset landscape. Follow up stages usually include spying once in the network, data encryption and eventually, the ransom demand and possibly extortion.
These are precisely the steps that the Ryuk operators are said to have followed in their attack on Epiq.
The Fall Out Remains to Be Seen
Epiq is choosing to be optimistic, told Brett Callow, a threat analyst at Emsisoft, that “there’s “no evidence the attack resulted in any unauthorized transfer, misuse or exfiltration of any data.” However, Callow advises there’s no way to know the state of Epiq’s data without a full forensic investigation. A cursory evaluation can’t reveal whether there has been underlying compromise, especially if the attackers have been present in the network for any length of time (dwell time). Callow also notes that he believes “it is unlikely data was exfiltrated, because the Ryuk group is not known to be one that steals data.”
Companies don’t always reveal if they’ve suffered a ransomware attack, resulting in delays in customers becoming aware that their data may be compromised. Among other threats, uninformed customers are at higher risk of new spear-phishing attacks.
One phishing attack was all the attackers had to carry out to take down Epiq’s entire network. More proof that network health and security must be priority one. It’s foolhardy to rely on third party security such as that of a data center or cloud provider. It’s also recommended that companies segment data separately so that if one area become infected, the damage is contained and can’t spread to other areas of the network. It sounds a lot like what every citizen is experiencing with virus concerns these days and the comparison is fitting.
Possible Small Chance of Recovery Remedy from Emsisoft
Epiq hasn’t yet revealed if they paid the ransom or not. But for them and other companies in a similar boat last year, Emsisoft offers some possible assistance in decryption. They’ve said there’s a small chance that they may be able to recover files encrypted by Ryuk.
How Does Virsec Help Businesses Protect Themselves from Ryuk?
Defense is good, but offense is better. In a dire situation, any offer of assistance is welcome. But better than having to resort to hoping you can find a way to decrypt ransomed files is not having your files encrypted in the first place.
Steps to Block Ransomware
- Follow best security practices
- Educate employees about phishing – this maybe the best preventative measure you can take
- Enable two-factor authentication on network devices and systems
- Follow password management policy that enforces regular updates with strong password requirements
- Ensure your third party vendors follow your security standards
- Implement a reliable back up and recovery system, protected from network access
- Protect applications and memory
Protecting Applications – Virsec’s Unique and Effective Application, Runtime and Memory Protection
Virsec takes a unique approach to guard-railing your applications and countering a broad spectrum of cyber attacks, including ransomware attacks.
Only Virsec Security Platform Delivers:
- Protection of application workflows, processes, file systems, libraries, memory and more at runtime
- Precise attack remediation and automation early in the attack cycle without need for expert analysis or machine learning
Deterministic threat detection based on request deviations initiated by malicious code, remote hackers, files and trusted processes no matter how attacks originate.
Further resources:
Solution Brief: Ransomware Protection
Solution Brief: Protection Against Advanced Web Attacks
The Year of Rising Ransomware, Ryuk Wields its Own Unique Nastiness
MegaCortex Ransomware Worsens — Hackers Change Users’ Passwords & Make Blackmail Demands
MegaCortex Malware Strikes Business Networks, Does Damage Both as Ransomware and Disk Wiper
Maze Ransomware Attacks Surge in 2020, Demand Ransom, Expose Data
Sources: