Ryuk – pronounced “r-ee-y-oo-k“ – is originally the name of a character in a popular Japanese comic book series, and also appears as that character in the anime and manga series “Death Note.” A demon of death, it’s fitting that the Ryuk name describes a nasty piece of ransomware circulating around the web.
We’ve seen a lot of ransomware attacks this year, more than prior years combined, and each of them has its own twisted method of bringing destruction. Ryuk is no exception, not just because of what it does but in the unique way in which it infects systems and networks and the problems that causes.
At just around 15-16 months old, Ryuk is young for a ransomware strain to gain this much attention this quickly, which means it’s serious. It’s a threat hanging over organizations that will continue to increase going into 2020.
Something Wicked This Way Comes
Relatively new on the scene, Ryuk was first discovered in August 2018 and became notorious when it struck Tribune Publishing newspapers last Christmas. On Christmas Eve, the night only Santa should be working, bad actors were busy invading Tribune servers. The paper at first thought it was experiencing a server outage but soon realized it was worse than that and they were a victim of a malware attack. Their data was encrypted and operations interrupted. They quarantined the servers but by then the infection reappeared and wasn’t contained. Security patches put in place by security staff were not adequate and when the servers were brought back up, Ryuk spread and re-infected other network systems.
Tribune continued to print its paper, though they were delayed and some ad sections were missing. It took some time, but Tribune recovered.
Another company, cloud hoster DataResolution, also suffered an attack from Ryuk, reported by Brian Krebs, security researcher. As with previous victims, their tactic was to shut down their network while working on damage control. They too have made progress in recovery but it’s taken time. Neither company mentioned whether they paid the ransom demand but given their recovery times were not quick, it would seem they didn’t pay.
What’s Unique About Ryuk?
Ryuk conducts a practice that’s being called “Big Game Hunting.” This is the practice of cyber criminals going after the larger organizations that have deep pockets, seeking to get a big ROI for themselves. Before the attack on Tribune Publishing, Ryuk had made other enterprises their victims globally, demanding ransoms ranging from 15-50 Bitcoins (BTC). At the time, this was in the range of $97,000 and $320,000 USD.
Pursuing large targets requires more finesse in putting together custom campaigns in order to be effective. A random approach to see what sticks – “spray and pray” – doesn’t work when your goal is Big Game Hunting. Typically a Big Game campaign is rolled out in stages, perhaps beginning with a phishing attack (as many ransomware attacks do). They seek to gain user credentials to get into the organization’s network where they can then survey the asset landscape. Follow up stages may include spying once in the network, data encryption and eventually, the ransom demand and possibly extortion.
Organizations are cautioned that among ransomware threats, Ryuk is the most expensive. Ryuk attackers demand about 10 times the average amount, though they claim their ransom amounts are negotiable. Researchers think more than one criminal group may be operating here, considering the ways ransom payments can apparently be arranged.
Last October, Ryuk struck three hospitals in Alabama so forcefully that they had to turn patients away, treating only the most dire while going in to manual operations mode. The attacks infected three medical centers all operated by the DCH Health System. Even once the attack was over, patients were required to confirm upcoming appointments and ambulances were redirected to other hospitals.
Even Malware Can Have Bugs – And They Make Things Worse
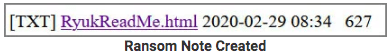
Ryuk invades networks and enjoys dwell time for days or months after the initial invasion. During that time, the attacker has time to take stock of the business’s critical systems and make plans accordingly. But even in cyber crime, things don’t always go smoothly. The bad actors appear to be having trouble with their encryption (decryption) process.
A feature of Ryuk that may not be as well known is that it can partially encrypt files. For files larger than 54.4 MB, Ryuk encrypts parts of the file instead of the whole, moving quickly, doing its encrypting before people notice. Files aren’t removed or damaged.
But a problem emerged when companies attempted to decrypt their files. Once the ransom was paid, desperate to get their data back, companies found the process of restoration was buggy and didn’t work effectively, causing their data to be corrupted or lost. Security researcher Emsisoft reports that Ryuk’s decryptor tool increases victims’ risk because it’s broken and not able to deliver data back to the many organizations hit by the malware, including government agencies, healthcare services, schools and private businesses.
Victims also sometimes found the attackers to be uncooperative. In ransomware attacks at large, sometimes the perpetrators are almost absurdly solicitous in their offers to “help” with the process and sometimes they don’t follow through on their end of the so-called bargain.
Emsisoft is offering a decryptor to help in such situations where organizations have paid ransoms but can’t retrieve their data, either because the perpetrator’s decryption method doesn’t work or is buggy or they aren’t cooperating. Emsisoft recommends contacting them first for their decryptor if you’ve suffered a Ryuk attack recently, before trying Ryuk attacker recommendations. But they caution that it won’t work unless you still have backups of your encrypted data. The Ryuk decryptor has often deleted or destroyed files rather than restored them.
“Please understand that this will only work if you still have copies or backups of your encrypted data, as the Ryuk decryptor will usually delete files it thinks were decrypted properly,” Emsisoft said. “Our tool will enable you to safely recover your data whereas the tool supplied by the bad actors will not.”
From Whence Does Ryuk Come?
Despite its namesake being from Japanese entertainment, Ryuk does not hail from Japan. Apparently it’s not uncommon for cybercriminals to choose handle names based on favorite anime and manga characters.
Learning the origin of malware gives insight into the attack as well as into the bad actors behind it, both of which are useful in mounting a defense. Check Point discovered a connection between Ryuk and the Hermes ransomware strain, as they shared similar code and structure. Subsequent to code analysis, many believe Ryuk likely came from the Lazarus Group, the same North Korean APT (advanced persistent threat) group behind Hermes ransomware. North Korea’s Lazarus Group is also believed to be behind the WannaCry ransomware malware.
Also, North Korea is in dire need of funds and the higher ransom amount aligns with the theory that they are the malware’s creators.
What Can Businesses Do to Protect Themselves from Ryuk?
- Follow best security practices
- Educate employees about phishing – this maybe the best preventative measure you can take
- Enable two-factor authentication on network devices and systems
- Follow password management policy that enforces regular updates with strong password requirements
- Ensure your third party vendors follow your security standards
- Implement a reliable back up and recovery system, protected from network access
- Protect applications and memory
Protecting Applications - Virsec’s Unique and Effective Application, Runtime and Memory Protection
Virsec takes a unique approach to guard-railing your applications and countering a broad spectrum of cyber attacks, including ransomware attacks.
Only Virsec Security Platform Delivers:
- Protection of application workflows, processes, file systems, libraries, memory and more at runtime
- Precise attack remediation and automation early in the attack cycle without need for expert analysis or machine learning
Deterministic threat detection based on request deviations initiated by malicious code, remote hackers, files and trusted processes no matter how attacks originate.
Further resources:
MegaCortex Ransomware Worsens — Hackers Change Users’ Passwords & Make Blackmail Demands
MegaCortex Malware Strikes Business Networks, Does Damage Both as Ransomware and Disk Wiper
LockerGoga Ransomware Slams Industrial Firms in Europe with Devastating Impact
Sources:
https://www.msspalert.com/cybersecurity-breaches-and-attacks/ransomware/buggy-ryuk-decryptor-risks/
https://www.eweek.com/security/how-enterprises-can-avoid-the-ryuk-ransomware-with-right-strategy