This blog explains the critical impact Remote Code Execution vulnerability in the Apache ActiveMQ message broker software and the threat it poses to organizations. We provide an in-depth analysis of the vulnerability and advanced threat techniques like Living off the Land Binaries (LOLBin) malware that could be used by Threat Actors and the attacker's activities in different kill stages. Finally, the blog summarizes how the Virsec Security Platform (VSP) protects against these threats.
Background: On October 27th, 2023, the US-CERT’s National Vulnerability Database (NVD) disclosed a remote code execution vulnerability, CVE-2023-46604 (Critical Impact) in versions up to and including 5.15.15, 5.16.6, 5.17.5, and 5.18.2 of Apache ActiveMQ. Apache ActiveMQ is an open-source message broker software that implements the Java Message Service (JMS) API. It provides a communication platform for connecting distributed applications, allowing them to exchange messages asynchronously. Over 4300 companies worldwide use the Apache ActiveMQ message broker.
Exploitation Risk: Several versions of Apache ActiveMQ message broker software are vulnerable to Remote Code Execution. The vulnerability may allow a remote attacker with network access to a broker to run arbitrary shell commands by manipulating serialized class types in the OpenWire protocol to cause the broker to instantiate any class on the classpath. As we know, any remote code execution vulnerability presents Threat Actors with a huge opportunity to infiltrate enterprises. Having penetrated the targeted workload, a Threat Actor can go on to perform lateral movement and initiate various malicious actions, including data exfiltration, credential theft, ransomware, denial of service, crypto mining, and botnet activities.
In-Depth Analysis: On Oct 27th, Rapid7’s MDR Response Team identified the exploitation of Apache ActiveMQ message broker in two different customer environments. In both instances, the Threat Actor attempted to deploy ransomware binaries on targeted workloads. Based on the ransom note and available evidence, Rapid7 attributed the malicious activity to the Hello Kitty ransomware family. A look back into the release history of Apache Active MQ shows that version 5.15, which was released on June 27, 2017, reached the end of support on March 9, 2022, whereas version 5.16, released on June 25, 2020, reached the end of support on March 18, 2023. Since the threat posed is so high, the Apache ActiveMQ community departed from precedent and made a special release for both these versions on October 25, 2023.
Advanced Threat Techniques: Given the inherent weakness in the typical EDRs’ ability to deal with LOLBin (Living off the Land Binaries) malware, threat actors prefer to use LOLBin Malware instead of precompiled malware that can potentially be analyzed in Sandboxes. By contrast, LOLBin malware is extremely hard to analyze in sandboxes because it leverages legitimate OS runtime utilities like bash and awk to execute commands, manipulate permissions, gather process information, extract credentials, access SSH private keys and known_hosts files, encode and encrypt data, inspect bash history, and even remove itself. Many legitimate software utilize such OS utilities, making it very difficult to distinguish between legitimate software and malicious software.
Kill Chain: We can divide the attacker’s activities into five stages: reconnaissance, persistence, weaponization, exploitation, and exfiltration.
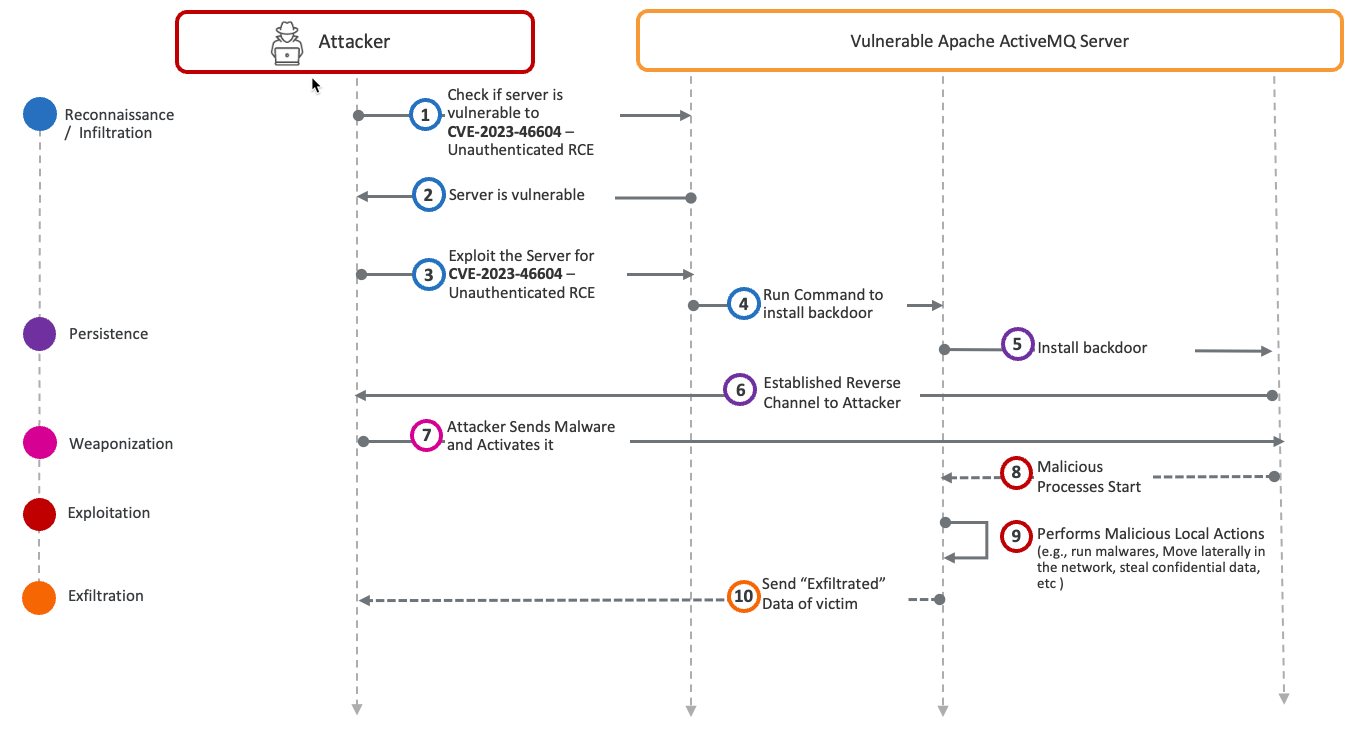
During the reconnaissance stage, Threat Actors leverage tools like Shodan to find enterprises that host vulnerable workloads. On successful infiltration, the attacker executes some LOLBin commands to establish a reverse channel for control, as shown in the persistence stage. In the weaponization stage, the attacker deploys second-stage malware (such as LOLBin scripts) for further reconnaissance, lateral movement, data exfiltration, etc. In the exploitation stage, the attacker performs malicious actions like lateral movement and data theft. Finally, in the exfiltration stage, critical data is sent back to the Threat Actor’s command and control center.
How VSP Protects: The Virsec Security Platform (VSP) plays a crucial role in this scenario. It identifies, within milliseconds, any code executed by the attacker as early as in the reconnaissance stage as being influenced by the attacker and therefore, malicious.
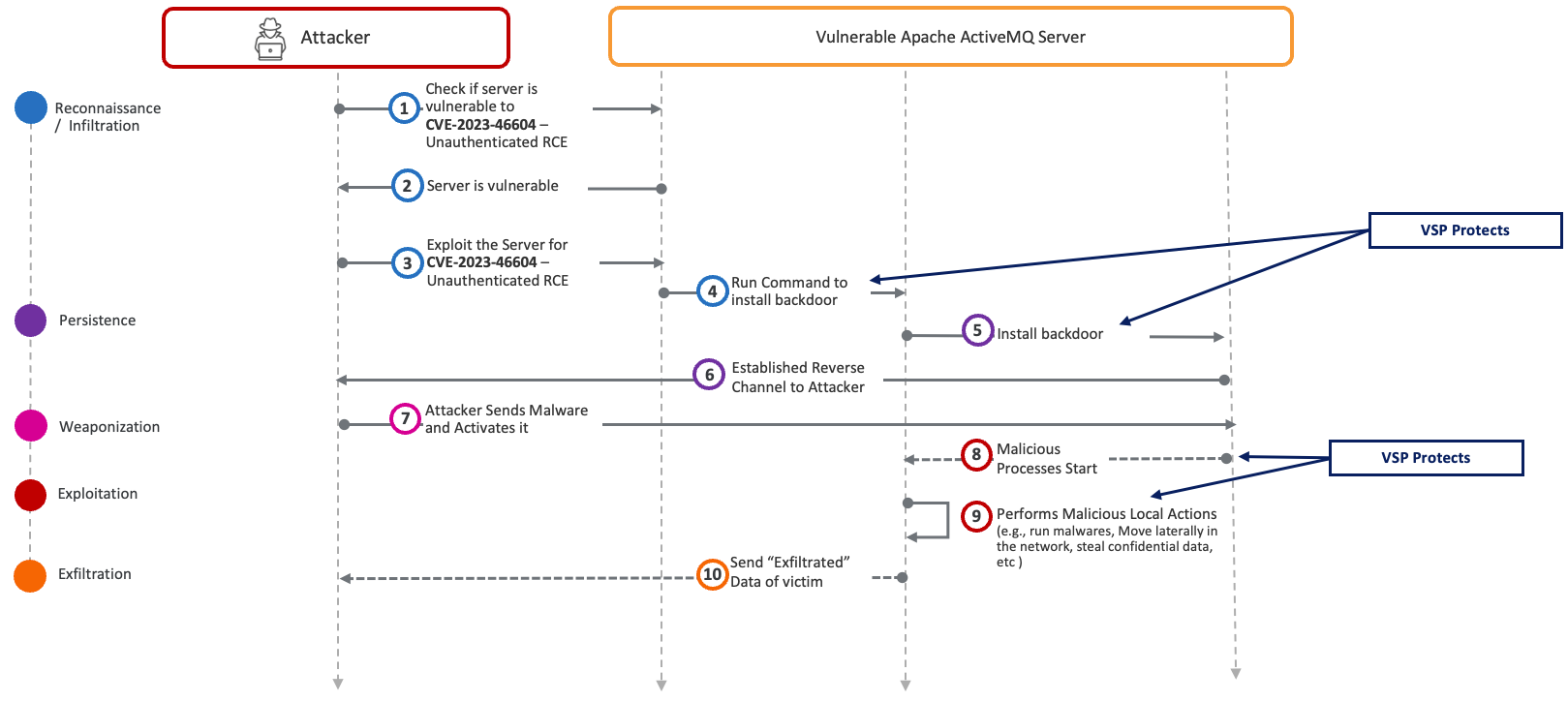
Even before the malicious code runs at Step 4, VSP’s Application Control Engine recognizes that no legitimate application is authorized to perform such actions. As a result, VSP safeguards the victim server by taking protective measures, such as terminating the user’s session, restarting the Apache ActiveMQ server, or closing the network socket used for communication with the attacker’s control center.
Demonstration: Watch this video illustrating how the Virsec Security Platform (VSP) thwarted Threat Actors that targeted these vulnerabilities at https://youtu.be/znfRP-X48kE.
Key Takeaways:
- Enterprises must have a strategy for dealing with unknown vulnerabilities that pave the way for known or unknown cyber-attacks. One way forward is to respond promptly the moment a Remote Code Execution vulnerability is published. The alternate way forward is to a compensating control and not live in constant fear. Threat actors are a constant threat, and the question isn’t if they will take advantage but when.
- The Virsec Security Platform (VSP) is a proactive compensating control that cuts the threat actor’s dwell time to milliseconds. This means that the enterprise is protected even when it cannot apply software patches promptly.
For more information about Virsec’s VSP Platform, visit our website at www.virsec.com
For more information about the Virsec Security Platform (VSP) and how we protect vulnerable legacy workloads, visit www.virsec.com.
Don't miss our security insights, and subscribe to our blog now.