You can’t stop what you can’t see. And attackers have found an area to exploit that conventional cyber security tools cannot see. This area is applications themselves, during runtime and all that involves, including files, processes, libraries, memory usage, and web inputs. This also includes process memory and entire server workloads housing the applications. All are vulnerable and falling prey to attacks on a daily basis.
Previously, runtime was a black box, hidden to businesses and not really thought about. It’s become a perfect place for attacks to play out in stealth mode, under the radar. They come seemingly out of nowhere, without warning or any ability to see them coming. This has stymied current preventative tools.
For decades, security tools have used backward-looking methods, such as signatures that could identify previously known attacks. But that meant that to mount an effective cyber defense, businesses would need to have prior knowledge of the same attack, or just plain get lucky and guess. And guesswork is hardly a recipe for success in any endeavor.
If you have a signature or rule to identify a cyber threat, then you can stop it, but the caveat is that it hasn’t changed since the last time your system saw it. And how often does that happen? This method is inherently unable to look forward or prevent previously unseen attacks.
Cyberattacks Playing Out in Real Time, Runtime, All the Time
Ransomware
In December 2019, the city of Pensacola, Florida, was struck by Maze ransomware operators. The attack took their phone systems, email servers and online billpay systems offline. The attackers requested $1 million in ransom. The exploit was accompanied by the Maze group’s signature threat to release files publicly if payment wasn’t received. Typical of Maze operators, they made good on the threat and posted between six to 10 percent of the data they had taken from Pensacola’s network.
The practice of revealing stolen data has become so commonplace the FBI now advises companies to make caches of decoy data for attackers to go after instead of the real thing.
Data Breaches
In 2018, Marriott Hotels experienced a different kind of attack in the form of a massive data breach. Full details aren’t known but when their CEO testified before the United States Senate, he shared some additional information. By Fall of 2018, Marriott had learned their data had been accessed, encrypted and likely stolen. Five hundred (500) million guest records (some duplicates) were breached, some containing sensitive info such as credit card data.
The business first became aware of the hack after a security tool noticed an unusual database query in the Starwood network. The tool was monitored by Accenture, which had been managing IT for Starwood prior to the merger with Marriott. A user with administrator privileges had made the database query. But a check showed that the user’s account was not the same person who had made the query. Someone else had usurped control of the account.
What’s more, the attack had been going on undetected for an astounding four years. This dwell time is enormous. The attackers gained access secretly and remained inside to explore internal servers. With escalated privileges, they moved to other systems and plotted their strategies year after year.
It’s been nearly two years since Marriott experienced one of the largest breaches on record, and they are still struggling with the aftermath. In August 2020, the United Kingdom brought a class action lawsuit against Marriott on behalf of former guests seeking compensation. Multiple other attacks such as these take place on a weekly basis.
Cyber Attackers Find Creative Ways Into Company Systems
Attackers are finding ways into the heart of business networks. Phishing is the most common method of entry at end points. But ultimately, regardless of the entry point, the attackers’ goal is to find their way deeper, to servers and applications. There they can exfiltrate sensitive data and/or launch damaging malware in runtime.
The Maze attack on the city of Pensacola likely initially invaded the municipality’s systems via phishing emails, a typical method for this group. They present their phony emails as official entities such as tax collectors, postal services or government agencies. Once inside however, their ransomware brought down multiple applications that help run the city.
As noted above, most security tools have treated application runtime as a black box. Advanced attackers know this and are exploiting this gap with fileless, in-memory, zero-day attacks. They use a range of techniques, aware that these activities fly below the radar of conventional security. Most of these conventional products operate before or after application runtime, but not during. This makes runtime is the new security battleground.
Attackers, of course, know this and are very adept at obfuscating attacks and using new techniques we haven’t seen before. They are also increasingly skilled at using fileless and memory-based techniques that have no discernable footprint from the outside. The attacks weaponize only as code executes.
Some tools look for clues after malicious code may have executed. For example, there is much hype about machine learning and other capabilities of EDR (Endpoint Detection and Response) tools. But detecting attacks after the fact is usually far too little, too late. By the time you receive an EDR alert and trace the root cause, hours, days, months or more may have passed. The attackers are long gone, along with whatever data they stole.
What Can Be Done to Stop the Blindsiding?
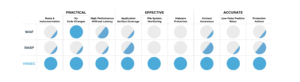
To effectively prevent runtime attacks you need full visibility into your applications as the code executes. Virsec is the first security solution to provide comprehensive protection of applications during runtime. Virsec’s patented AppMap® technology maps what an application is supposed to do. Virsec instantly detects and stops any deviations caused by illicit code or attackers as it executes – before damage is done. Virsec monitors all activity during runtime, including files, processes, libraries, memory usage, and web inputs.
Unlike probabilistic techniques, Virsec is deterministic, positively identifying real attacks without the noise of false alerts. Virsec prevents application workloads from being hijacked or infiltrated and protects memory, files, processes and data from the inside.
Our recent live demo details how a memory attack plays out in real time in a real attack scenario.
Learn how you can prevent your business from being the next victim of a ransomware attack or data breach. Download our free guide Five Essential Steps for Enterprise Application Security.