Virsec Security Research Lab Vulnerability Analysis
The Virsec Security Research Lab provides timely, relevant analysis about recent and notable security vulnerabilities.
1.1 Vulnerability Summary
Vulnerability in the Oracle WebLogic Server product of Oracle Fusion Middleware (component: Web Services). Supported versions that are affected are 10.3.6.0.0 and 12.1.3.0.0. Easily exploitable vulnerability allows unauthenticated attacker with network access via HTTP to compromise Oracle WebLogic Server. Successful attacks of this vulnerability can result in takeover of Oracle WebLogic Server.
Watch the video to learn more about this and other important vulnerabilities.
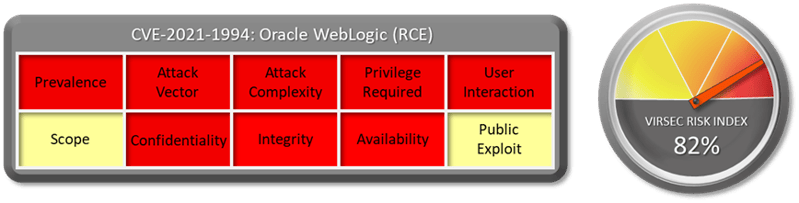
1.2 CVSS Score
The CVSS Base score of this vulnerability is 9.8 Critical as per NVD. CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H
1.3 Affected Version
Supported versions that are affected are 10.3.6.0.0 and 12.1.3.0.0.
1.4 Vulnerability Attribution
These vulnerabilities were discovered and reported by oracle.
1.5 Risk Impact
No exploits are available publicly. Oracle WebLogic Server is a Java EE application server currently developed by Oracle Corporation. Oracle acquired WebLogic Server when it purchased BEA Systems in 2008.
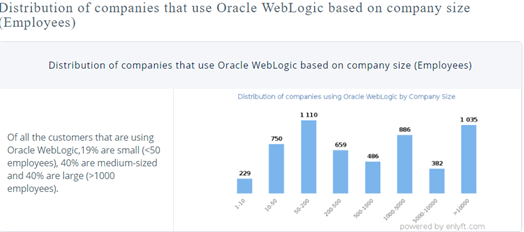
Weblogic first released their version in 1997 and since then it has been used by Top 1000 enterprise over a period of last 20 years and many of them continue to use same legacy stack. Any exploit of this vulnerabilities could lead to exposure of all sensitive data that resides on the server via backdoor which could be doing data exfiltration to CnC server.
1.6 Virsec Security Platform (VSP) Support:
VSP-Host monitors processes that are spawned which are not part of a set of whitelisted process. Any attempt to execute new command or unknown binary would be denied by VSP-Host’s Process Monitoring capability.
1.7 Reference Links:
Download the full vulnerability report to learn more about this and other important vulnerabilities.
Do you have a request for a vulnerability Virsec Security Research Lab to explore? Let us know!


