Satya Gupta, Founder and CTO, Virsec
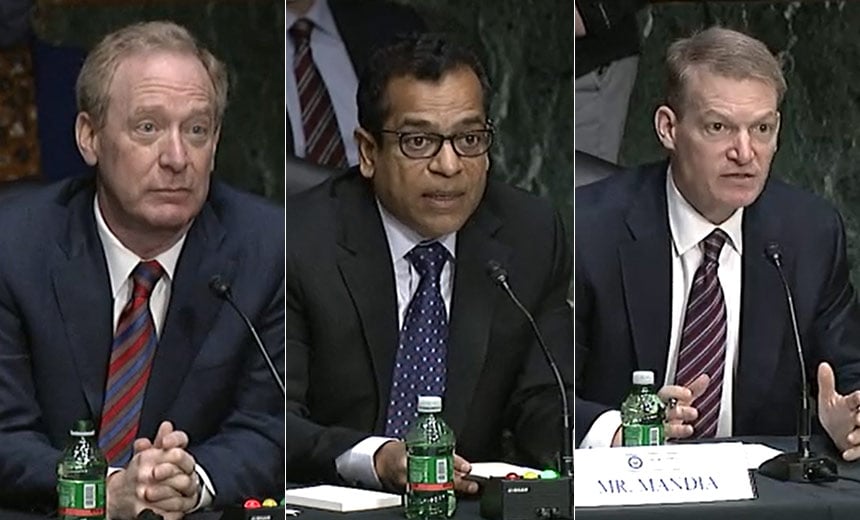
The US Senate Cyber Intelligence Committee held a hearing on the SolarWinds attack on February 24, 2021. Senator Warner (Chairman), Senator Rubio (Vice Chairman) and several other ranking Senators heard testimony from three cyber vendors, FireEye, Microsoft, and CrowdStrike as well as from SolarWinds – the victim and conduit for the broader supply chain attack. Three pieces of testimony stood out:
1. It was stated that it took thousands of hours of reversing the binary code of the Sunspot malware just to begin to understand what the malware did and develop a signature that could then be disseminated to other potential victims.
2. It was also stated that the attack was the culmination of an effort of about 1,000 bad actors working for at least six months from Oct 2019 to March 2020.
3. It emerged that about 18,000 enterprises including hundreds of US Government organizations became secondhand victims of the SolarWinds Supply Chain attack. These included many Fortune 100 enterprises in the US. All these victims risk losing intellectual property and economic dominance to a foreign adversary.
The Senate Committee concluded that because the foreign adversary had breached the thin red line of interfering with the sacrosanct software patching process, the attack amounted to an act of Cyber War on the US.
Comparing Testimony with Reality
As an experienced cyber researcher, I believe several facts stated by the cyber vendors are not accurate or misleading and should be examined further:
1. The Virsec Security Research team produced the equivalent of the Sunspot malware in only sixteen man-hours. This represents a tiny fraction of the time the so-called “army” of 1,000+ malware engineers had, working over a six-month period. The implication from the vendors was that this attack was highly complex, difficult to build, and therefore rare. As we demonstrated in our lab, this is simply not true.
2. Making a small cosmetic change in the malware code we developed, resulted in a completely different signature for the malware. Rather than spending thousands of hours on one piece of malware, the army of bad actors is likely producing thousands of variants, each being undetectable for months with current protection technologies that require prior knowledge.
3. If it takes 1,000s of hours to reverse malware code that takes 10s of hours to develop, then there is something gravely wrong with current cyber security technologies. If an attacker can produce malware 100 times faster than it takes to detect and analyze it, the existing knowledge-based approaches to cyber security will never keep pace and are doomed to failure.
4. While SolarWinds and Microsoft have been trading accusations, the vendors failed to inform the Senate about the root cause of the problem – a vulnerability in the code of the email server used by SolarWinds which allowed the attackers to first infiltrate and the dwell time undetected for months within the SolarWinds software infrastructure.
5. The invited vendors failed to shine a light on the real danger, that even one remote code execution vulnerability in the infrastructure of a software vendor puts the entire supply chain of that vendor at risk.
6. The vendors and the victim failed to disclose the presence of the Super Nova variant of backdoor malware that generates malicious code directly in memory. With no file being written to disk, there is no signature that can be checked to stop it. This type of fileless malware bypasses most security technology
For these reasons, we believe that the situation is much more serious than the testimony portrayed. It is relatively easy for bad actors (especially from nation states) to produce millions of unique malware variants that each have the potential to insert backdoors into software, which take knowledge-based tools months or longer to detect. We also believe that remote code execution vulnerabilities will provide ample opportunities for planting backdoors into any popular software that has an extended supply chain. In fact, hundreds of remote code execution vulnerabilities are reported into the NIST National Vulnerability Database each week.
Our entire economy runs on software, and it is imperative that we treat the SolarWinds incident with the full seriousness it deserves, or our security, intellectual property and economic dominance in the tech sector will become a thing of the past. Clearly, new technologies are needed to defend our nation because existing technologies and vendors cannot meet the challenge no matter how hard they try. Spending thousands of hours developing a signature for each of the millions of variants that can come out every day is simply a fool’s errand.
Seeing is Believing
As stated previously, our security lab spent an hour studying the CrowdStrike blog on Sunspot, and then only fifteen hours developing and fine tuning a Sunspot malware variant, that is as effective as the original, but has an entirely different signature. We then produced a demo in which we leveraged a remote code execution vulnerability in the Exim Email server code to infiltrate the software infrastructure. From there we deployed the Sunspot backdoor variant on the build server of a hypothetical software vendor to inject malicious code into the vendor’s application.
Given that hundreds of new remote code execution vulnerabilities are reported in open-source libraries and closed-source applications, along with untold numbers of undisclosed vulnerabilities, we feel that a motivated attacker can insert backdoors into the code base of thousands of software vendors.
The Need for Application-Aware Security
Next-generation application-aware cybersecurity technologies run along-side the application, protecting in much the same way that a GPS helps a driver stay on course during a journey. These technologies can spot immediately when either attacker-produced, or attacker-injected code starts executing. They do so without any prior knowledge or signatures of malware or its variants. By automatically hardening the protected application, these technologies can detect and terminate an attack before the attacker can breach their victim’s software infrastructure, even if the attacker has leveraged an undisclosed vulnerability for which no patch exists. This modern approach to cybersecurity also can eliminate the long dwell time of SolarWinds attack, where attackers stayed undetected from September 2019 to December 2020.
Government Action is Needed
As the Solarium Commission evaluates new requirements for cybersecurity, and Congress weighs possible legislation, we believe it is imperative that the industry stop repeating the mistakes of the past and move to a next-generation of security technologies. While legislation rarely (or effectively) mandates specific technology, we believe the seriousness of the SolarWinds attack, and similar ones certain to come, that the government take a much more proactive approach to cybersecurity and treat this type of cyber warfare as an immediate threat to our technological economy.
Virsec’s Application-Aware Workload Protection Technology
Virsec produces application-aware security controls that can keep any software application safe at runtime even if there are unpatched or unknown vulnerabilities. At its core, Virsec’s technology uniquely recognizes the instant attacker-produced, or attacker-influenced code attempts to execute. This is the critical point where the attack kill chain can be stopped, without prior knowledge, before damage is done.
Virsec will be happy to work with NIST to augment their otherwise carefully documented security controls in the specification 800-53R4 with application-aware controls. Virsec would also be more than happy to demonstrate the efficacy of application-aware security controls to technical experts that the Solarium Committee intends to rely on.
Download our Technical Brief: Taxonomy of The Attack on SolarWinds and Its Supply Chain