SC Magazine, June 25, 2019, with comments from Satya Gupta;
A fully patched Windows PC can spread malicious malware functions via Excel attachment
Microsoft issued a warning about malware that runs a remote access Trojan, triggered by an Excel attachment. The attachment spreads a macro that’s in turn runs the Flawed Ammyy remote access Trojan (RAT). To avoid this scenario, the Microsoft Security Intelligence team advises users to disable all macros.
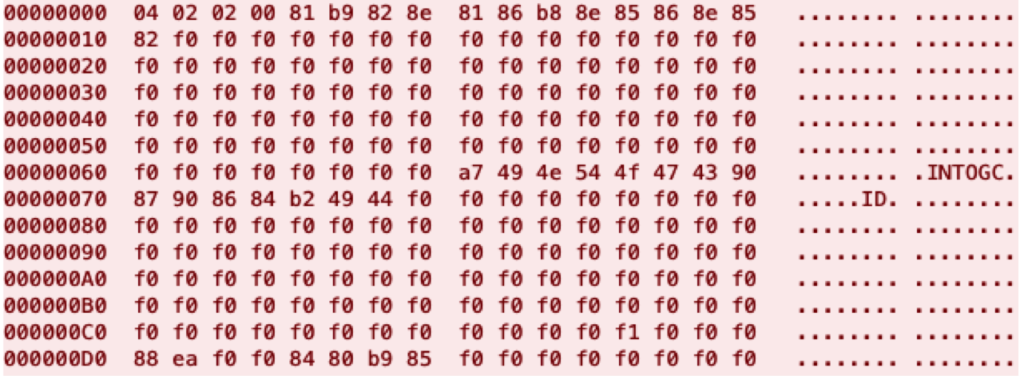
Microsoft warns FlawedAmmyy starts with email .xls attachment, runs in memory
“Anomaly detection helped us uncover a new campaign that employs a complex infection chain to download and run the notorious FlawedAmmyy RAT directly in memory. The attack starts with an email and .xls attachment with content in the Korean language.”
Once the .xls file is opened it “automatically runs a macro function that runs msiexec.exe, which in turn downloads an MSI archive.”
A digitally signed executable in the MSI archive is extracted and run, then decrypts and runs another executable in memory.
From there, that “executable downloads and decrypts another file, wsus.exe, which was also digitally signed on June 19. Wsus.exe decrypts and runs the final payload directly in memory.”
The final payload is FlawedAmmyy.
Macros provide too easy a path for malware to hitch a ride inside
Satya Gupta, CTO and co-founder of Virsec tells SC Magazine, “Excel macros have been associated with malware for a long time, but it’s still alarming for Microsoft to recommend disabling all macros – functions used routinely by millions of businesses. Microsoft needs to rethink its macro strategy as it has become an easy vehicle for malware to get into fully patched systems.”
Gupta notes that once attacks are in memory they’re mostly undetectable and leave few traces in the wake of an application’s execution. “Below the surface we also need a new approach to in-memory attacks that are being launched through these macros.”
Gupta adds, “However these threats get in the front door (and there’s almost always a way in…) once in memory these attacks are undetectable by most security products and leave few traces behind after an application is done executing.”
Microsoft already released “cookiejacking” patch recently, among many others
Earlier this month on June 11, Microsoft released a big security update regarding 16 patches it planned to release to address 34 vulnerabilities across multiple Microsoft products. Microsoft Windows, Office, Internet Explorer, .NET Framework, SQL Server, Visual Studios and more are among the products needing the patch. Nine (9) bulletins are rating critical and affect all Windows versions, plus Excel and Internet Explorer. A notable Internet Explorer patch addresses “cookiejacking,” where an attacker grabs a browser file (cookie) in order to obtain login credentials.
Hackers also aim to steal usernames and passwords credentials for well-known sites such as Facebook and Twitter. Users fall prey if they perform a click and drag action that moves an object into an HTML element the hacker controls. This deceptive trick is called clickjacking.
Read full Microsoft’s Disable macros to avoid FlawedAmmyy trojan article.
Further resources:
Blogs:
Microsoft Bluekeep Flaw Threatens Medical Devices, IoT
ZombieLoad Affects Data Centers and Here’s What You Can Do About It
White paper: White Paper: Caffeinated Networks Efficacy Testing of Virsec Security Platform
https://virsec.com/white-paper-making-applications-truly-self-protecting/
Newsletter: Current issue